HSBC Global Trade Pulse Survey
Article
Structured financing solutions for supply chains are increasingly important in offering treasury te...










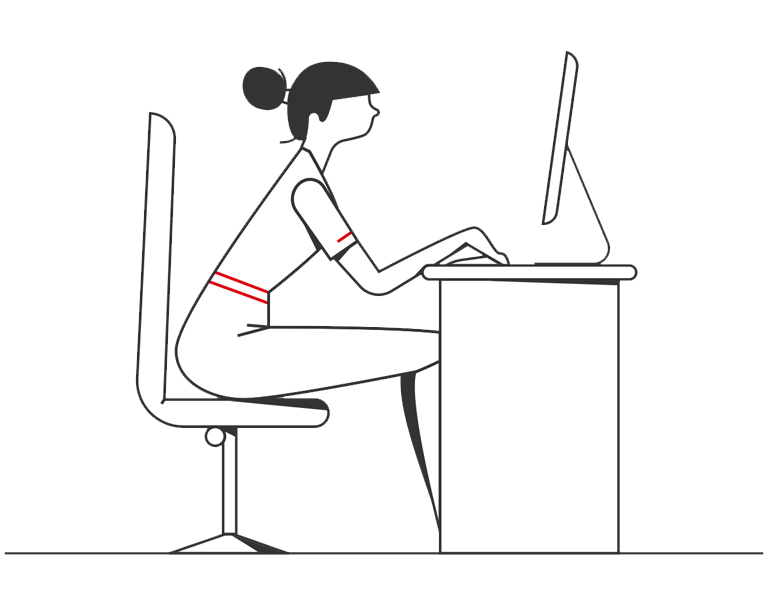
Improve working capital by unlocking funds caught in the supply chain, and manage incoming and outgoing cash flows more effectively organisation wide.